Cybercriminals don’t clock off.
While your team sleeps, eats, and unwinds… attackers are scanning, phishing, and sneaking in.
This is how active the threat is around the clock.

Cybercriminals don’t clock off.
While your team sleeps, eats, and unwinds… attackers are scanning, phishing, and sneaking in.
This is how active the threat is around the clock.

You’re focused on leveraging the latest technology for growth and innovation, but there’s a hidden risk that comes with it. The software, automated systems, and AI tools that power your business each have their own non-human identity (NHI). Managing these digital identities was a significant challenge even before the AI boom, but now, with intelligent agents capable of independent action, NHIs represent a critical threat that demands immediate attention.

Many people are getting better at spotting phishing attacks from outside sources. But what if the attack appears to come from within your own company? A recently discovered vulnerability in Microsoft 365 is being used to bypass traditional security, making it easier than ever for hackers to send you convincing fake emails that slip past your defenses.

As the digital world becomes increasingly complex, finding ways to protect personal and business information is more important than ever. Traditional passwords have long been the go-to solution for securing online accounts, but they come with a variety of vulnerabilities.
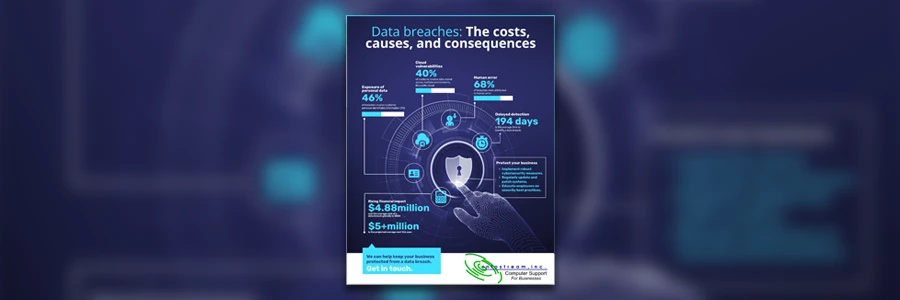
A data breach doesn’t just cost money. It damages trust and disrupts business. Plus, it can take months to detect. The risks are growing. Fast.

Cybersecurity has become a priority for businesses of all sizes, not just big corporations. Small businesses, often overlooked in the cybersecurity conversation, are now prime targets for cybercriminals. This blog delves into the reasons why small businesses are struggling more with cybersecurity today.

Threat intelligence platforms (TIPs) offer valuable insights to help detect and prevent breaches. However, fully utilizing them can be challenging without the right experience or expertise. The good news is that there are strategies to unlock the full potential of your TIP, turning it into a strategic asset that helps you stay ahead of cyber risks and prepare for future threats.

A data breach doesn’t happen all at once.
It happens step by step.
From a single click on a phishing email… to stolen credentials… and leaked customer data. Each stage puts your business at greater risk.
This is how breaches unfold, and the simple actions you can take to prevent them…
#CyberSecurity #DataProtection #BusinessSecurity
.wp-post-image { display: none; }

From phishing scams to ransomware attacks, the risks to your business are real.
And the consequences can be devastating.
If you think your business is too small to be a target, think again.
Acting today could save you time, money, and stress tomorrow.