Feeling drained by tech stress and constant distractions?
The way your workspace is set up has a bigger impact on productivity than you think.
From the tools you use to the way you sit, small tweaks can make a huge difference.
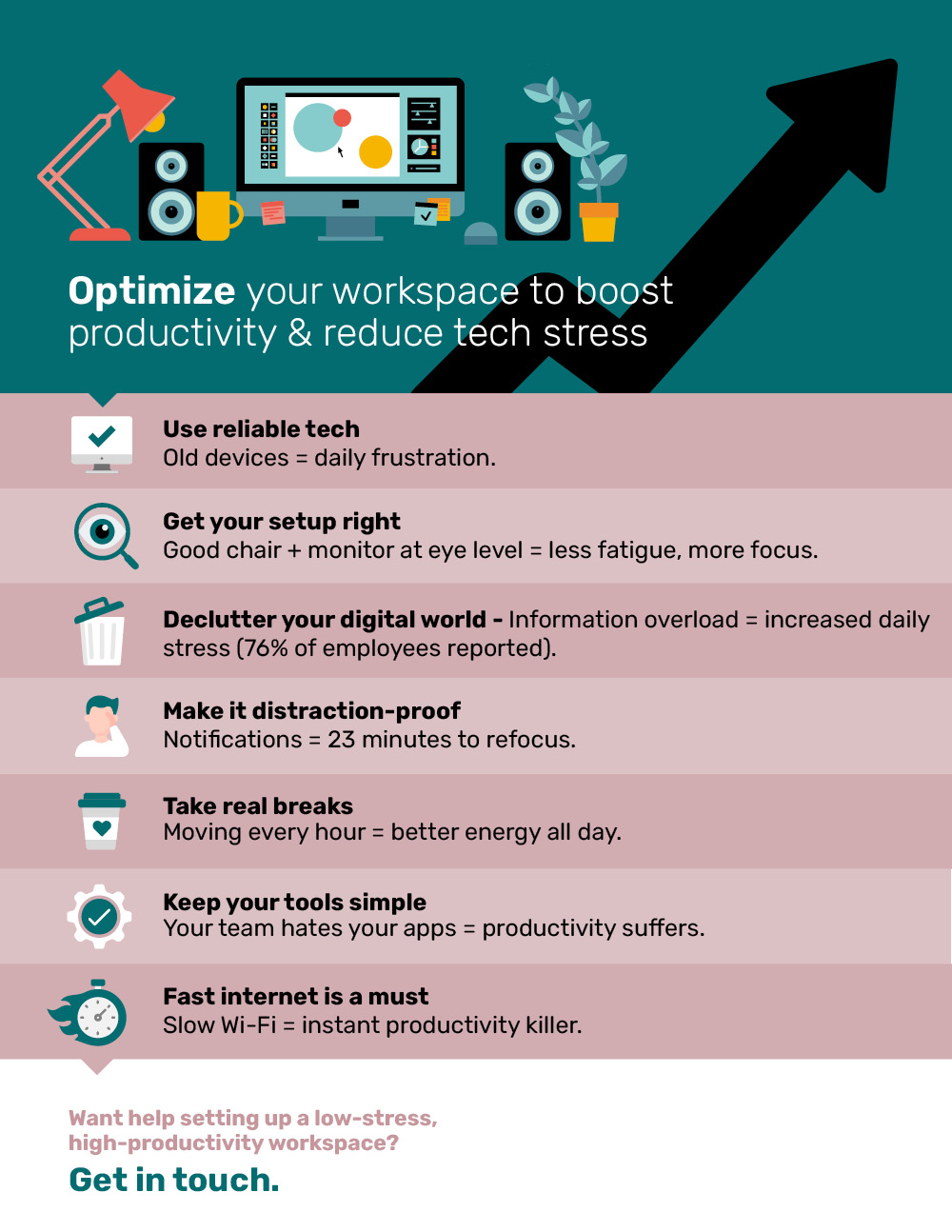
Feeling drained by tech stress and constant distractions?
The way your workspace is set up has a bigger impact on productivity than you think.
From the tools you use to the way you sit, small tweaks can make a huge difference.

Malware, phishing, and DDoS attacks are just the tip of the iceberg when it comes to digital threats facing modern businesses. This guide breaks down these risks and explains how to protect your business from them. Whether it’s using strong passwords, monitoring your network for suspicious activity, or educating your employees, taking these steps will help fortify your business against cybercriminals.

Discover essential best practices for effectively securing your mobile devices, from using strong passwords to using virtual private networks (VPNs) and keeping apps up to date. These simple steps can prevent costly data breaches and keep your company’s sensitive information safe from cybercriminals.

You know that Wi-Fi camera you just installed to see who’s at your business’s front door… is it possible it could present a risk to your data?
You’d be surprised. Here are the main security risks for all types of devices.
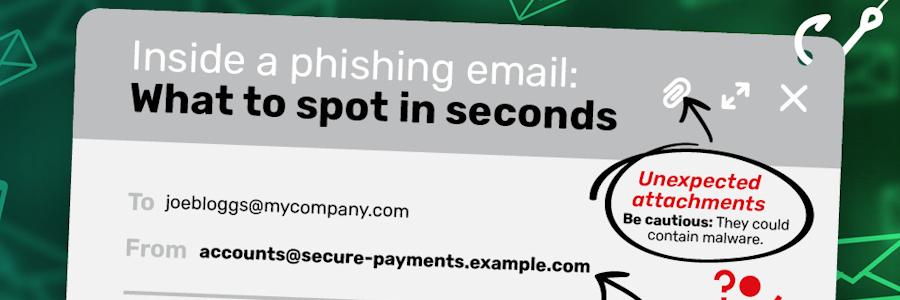
Phishing emails are getting SMARTER. They’re when cybercriminals pretend to be someone you trust, to get you to click a suspicious link.
Think you or your team could spot one in seconds?
Sometimes the clues are obvious. If you know where to look…

Cybercriminals are now using innocuous office devices such as printers and scanners to launch phishing attacks without needing to hack into your email account. Learn how to spot and stop this new trick to keep your workplace safe from phishing scams.
How Does a Cybercriminal Break into a Business?
It’s not always the high-tech hacks you hear about on the news. Sometimes it’s much simpler. And closer to home.
Look at these 20 common ways businesses get hacked. Some might surprise you.

Cybercriminals don’t clock off.
While your team sleeps, eats, and unwinds… attackers are scanning, phishing, and sneaking in.
This is how active the threat is around the clock.

You’re focused on leveraging the latest technology for growth and innovation, but there’s a hidden risk that comes with it. The software, automated systems, and AI tools that power your business each have their own non-human identity (NHI). Managing these digital identities was a significant challenge even before the AI boom, but now, with intelligent agents capable of independent action, NHIs represent a critical threat that demands immediate attention.