We live in a world where everything is at our fingertips. Cell phones and tablets mean we have our address books, email, calendars, and even data with us always. One of the most requested features is to be able to access the office from offsite and work on data and information without coming in to the office. This is a great way to stay productive while getting other things completed off the checklist.
There are several methods for getting access to your data remotely, but one of the more common methods is to gain full control of a computer in the office. This gives you all the benefits of sitting at your desk, without having to worry about if the Interstate will be a parking lot today. There are three main methods for configuring remote access to your computer. They all require some setup ahead of time, so the discussions on how to remote in need to be decided ahead of the need for the remote access.
The first option is to use a built-in tool with Microsoft called RDP. This tool provides very quick response to the remote computer once connected and you can practically forget that you are working on a different computer than the one you are sitting at. It comes built in to every Microsoft Windows computer, so there is no additional cost to it. But, it is not very secure. Hackers know it comes built in to every computer as well, so they are out there looking for computers with RDP exposed to the Internet as possible targets. When they find one, they can repeatedly attack it until they guess the right password, and they have full control of your computer to do whatever they want. Your protection is limited to strength of your password, and since many people still don’t change their password, that’s just not good enough. There are ways to limit some of this exposure, but this involves limiting where you can remote in from, which limits the usefulness of this configuration.
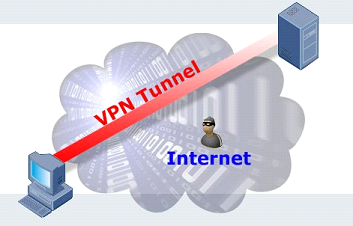
The second option then, is to setup a VPN tunnel. A VPN creates a “Virtual Private Network”. In effect it connects your remote computer or location to your office network while preventing anybody from seeing the information you are transmitting. Hackers don’t have the required information to configure a tunnel for themselves, so they can’t see your information and try to steal it. Once you are connected to your network through the VPN, you can use RDP as before, but using local connections rather than Internet connections, and the hackers are blocked from finding your computer. The addition of the VPN does require some extra tools. A VPN capable firewall needs to be in place, and a security certificate needs to be purchased. Also, a VPN takes more skill to implement and some additional training for end users is usually necessary.
The third option would be a product called an RDGateway. This hides the RDP traffic across the Internet by using secured web traffic. This keeps the hackers from being able to attack it because it looks like every other website out there that requires a username and password. Once you reach the RDGateway, the traffic is converted to RDP but that is again an internal route, so it stays safe. This keeps the speed of the RDP technology, but requires advanced technical knowledge to setup securely.
Finally, there are 3rd party tools that move completely away from the RDP technology. These are where names like LogMeIn, and GoToMyPC fit in. They install an application on the computer that is configured to send remote connection information to a website on the Internet. You log in to that website and you can then take control of that computer. Because you are using somebody else’s webserver in most cases, this usually requires a recurring fee for them to maintain their equipment and software. Hackers will not even know you have remote access available, so this is a very secure method of access. One downside to this technique is that these tools tend to not respond as crisply as RDP methods, so they can be a bit “laggy” to respond.
Remote access to computers is one of the more useful technologies. It has been around for quite a while, but recently it seems to have reached a stage where more and more people are finding a use and a need for it. All the options presented here have their uses and niches. Across the multiple networks InfoStream supports, we have found situations where each of these options has been chosen to meet the needs of various clients.
If you find yourself looking for the right solution to expand your abilities to work remotely, please contact InfoStream or give us a call at 561-968-0046. We offer IT solutions and network support in Palm Beach.