Is your inbox already full of junk before you’ve even had your first coffee?
Firewall 101: What Every Business Should Know
Is your inbox already full of junk before you’ve even had your first coffee?
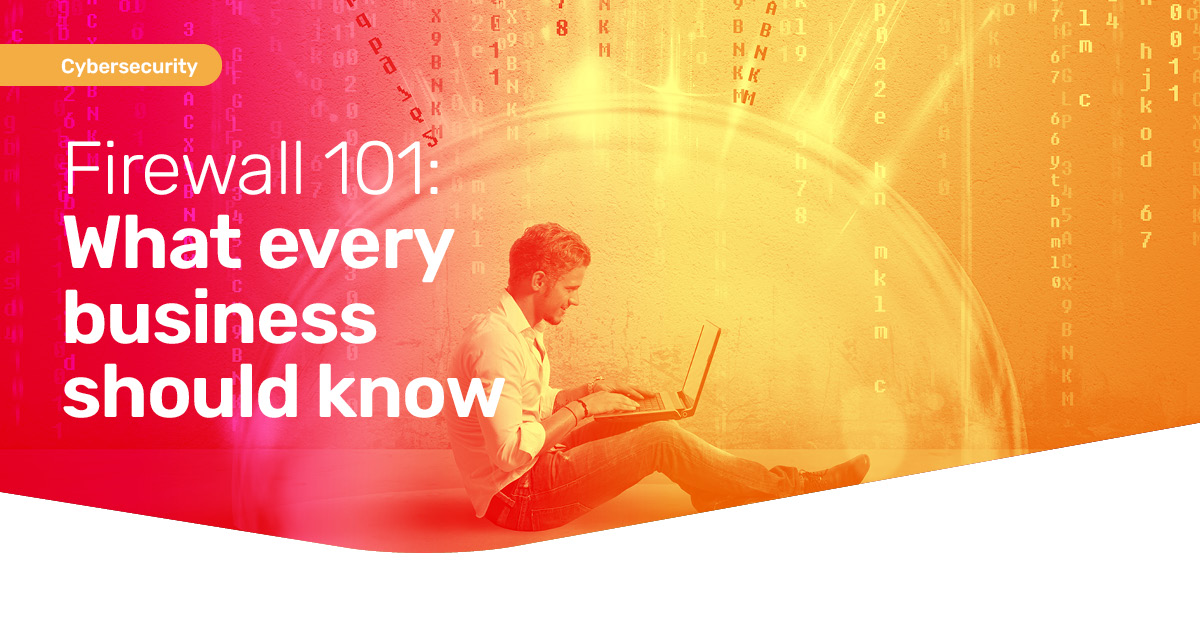
AI’s for more than writing posts or creating images.
It’s quietly transforming how businesses work. Saving time, improving communication, and even strengthening security.
The smartest companies aren’t asking if they should use AI… they’re asking how.

Think your business wouldn’t be a target for cybercriminals?
Think again.
Most attacks don’t start with Hollywood-style hackers. They start with simple mistakes.
Weak passwords. Missed updates. No backup plan.
These are five red flags that make businesses like yours an easy target (and how to fix them before it’s too late)…
.wp-post-image{display:none;}

Is your inbox already full of junk before you’ve even had your first coffee?

If your business is still juggling emails, lost files, and “final_final_v3” documents, Teams could be a game changer.
Yep, it does more than just video calls.
Our latest guide shows you how to use Teams as your digital office. Keeping your people connected, organized, and working smarter.
Download your free copy now.

If your business is still juggling emails, lost files, and “final_final_v3” documents, Teams could be a game changer.
Yep, it does more than just video calls.
Our latest guide shows you how to use Teams as your digital office. Keeping your people connected, organized, and working smarter.
Download your free copy now.

If your business is still juggling emails, lost files, and “final_final_v3” documents, Teams could be a game changer.
Yep, it does more than just video calls.
Our latest guide shows you how to use Teams as your digital office. Keeping your people connected, organized, and working smarter.
Download your free copy now.
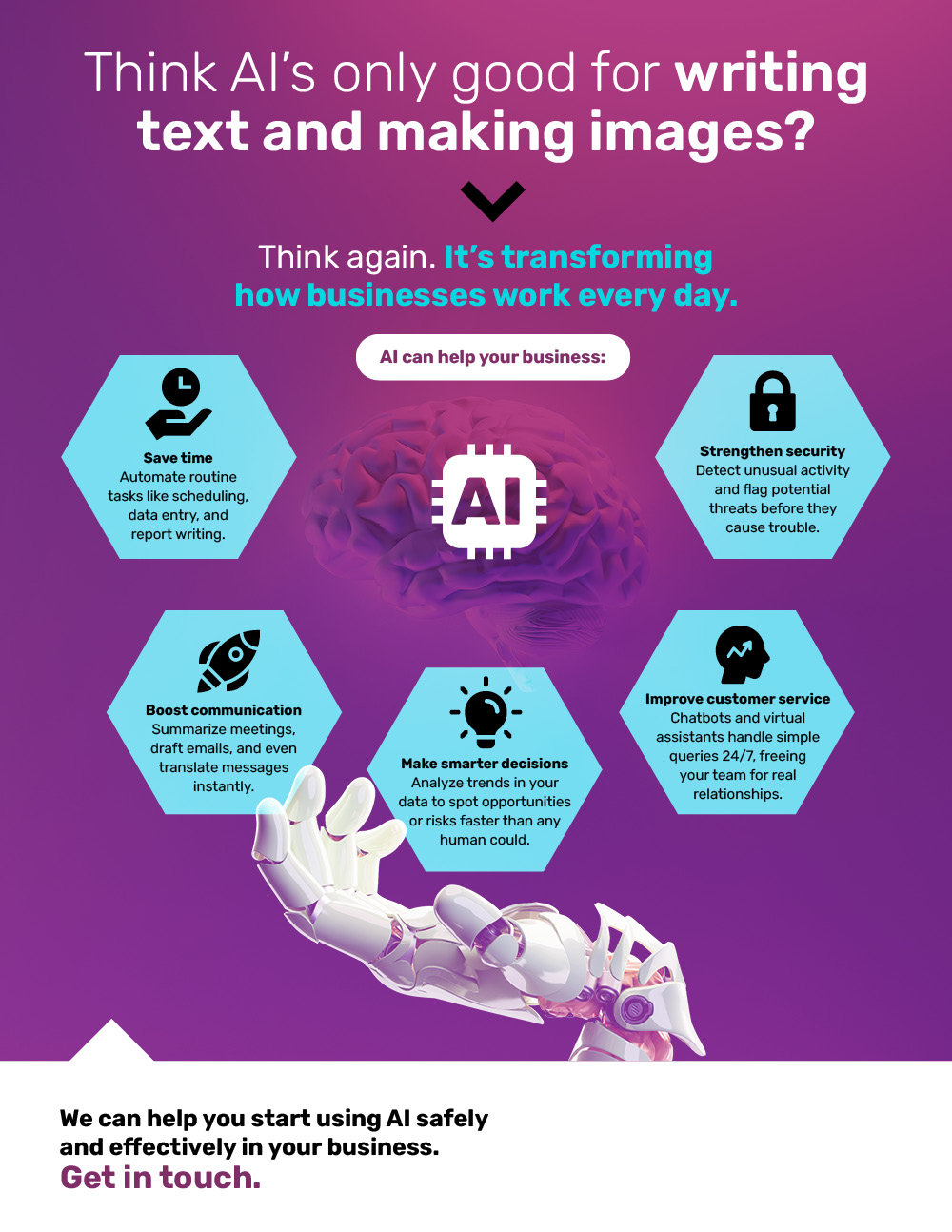
Is your IT support fixing problems before you spot them?
Or does it leave you waiting days for help?
Great IT keeps your business secure, productive, and always moving forward.
This is what it should look like…
.wp-post-image{display:none;}
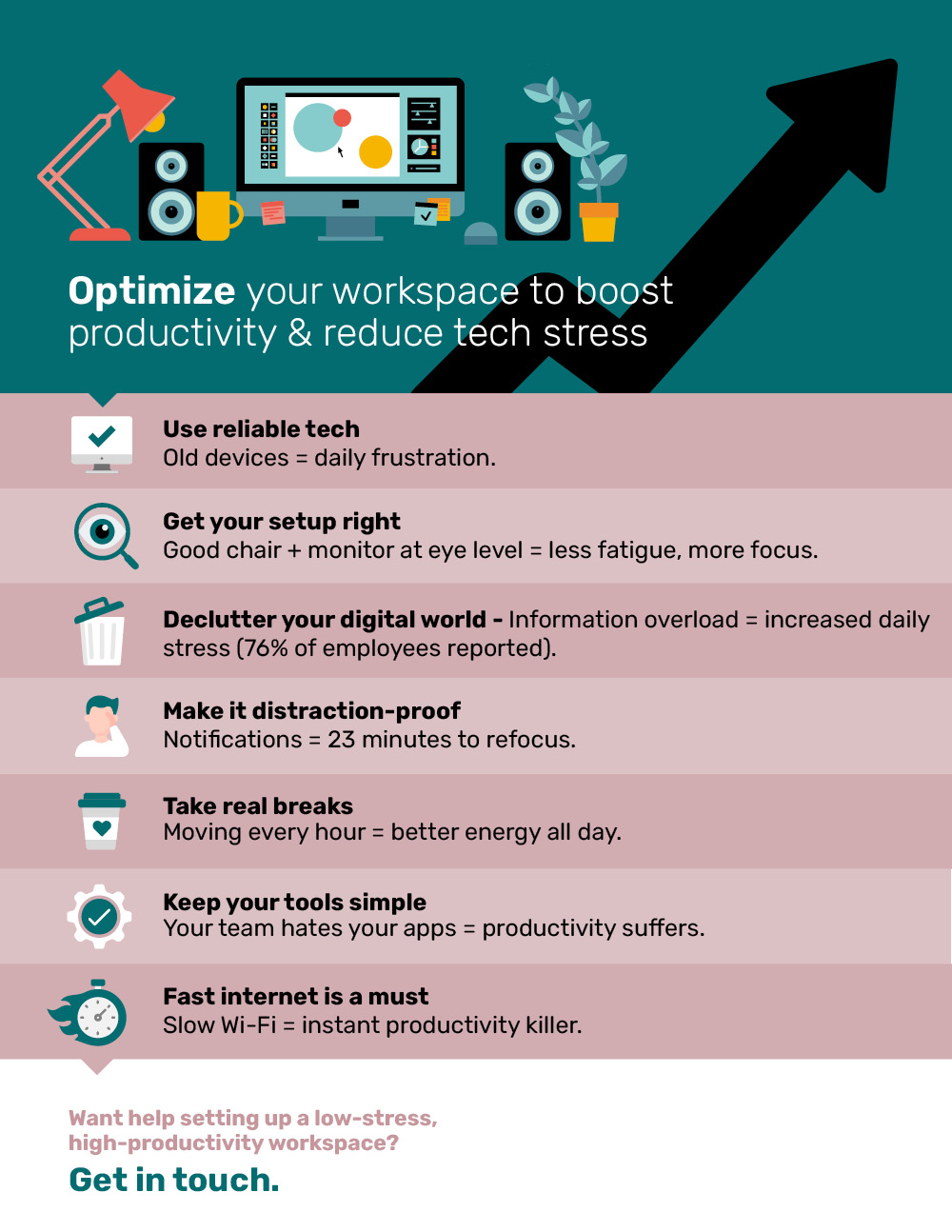
Feeling drained by tech stress and constant distractions?
The way your workspace is set up has a bigger impact on productivity than you think.
From the tools you use to the way you sit, small tweaks can make a huge difference.